The traditional boundaries that once confined us to a designated office space have blurred, giving rise to the era of hybrid work. As organizations embrace the flexibility of remote collaboration, a new set of challenges emerges, putting a spotlight on the need for robust cybersecurity measures.
When hackers plan their attacks, they are in search of a perfect entry point to your business. This point could be a website, software, or a networked device.
68% of organizations have faced one or more successful endpoint attacks resulting in the compromise of data and/or their IT infrastructure, reveals research by the Ponemon Institute. The study also highlighted that 68% of IT professionals observed an increase in the frequency of endpoint attacks compared to the previous year.
Endpoint security is the silent guardian of your digital realm, like a skilled locksmith ensuring that the doors to your virtual kingdom are locked tight against online threats. In this blog, we will explore the nuances of endpoint security and how it will protect your business.
What is endpoint security all about?
Endpoint security, also known as endpoint protection, is a facet of network security that encompasses various measures to safeguard a business network accessed by remote, wireless, or mobile devices like laptops, tablets, and phones. It is designed to protect these endpoints, whether in a network or cloud environment, from cybersecurity threats.
From traditional antivirus software, endpoint security has evolved to provide comprehensive defense against sophisticated malware and evolving zero-day threats. It serves as the frontline of cybersecurity, addressing risks posed by nation-states, hacktivists, organized crime, and insider threats. Modern endpoint protection systems swiftly detect, analyze, block, and contain attacks, collaborating with other security technologies for enhanced visibility and faster response times.
What are endpoint devices?
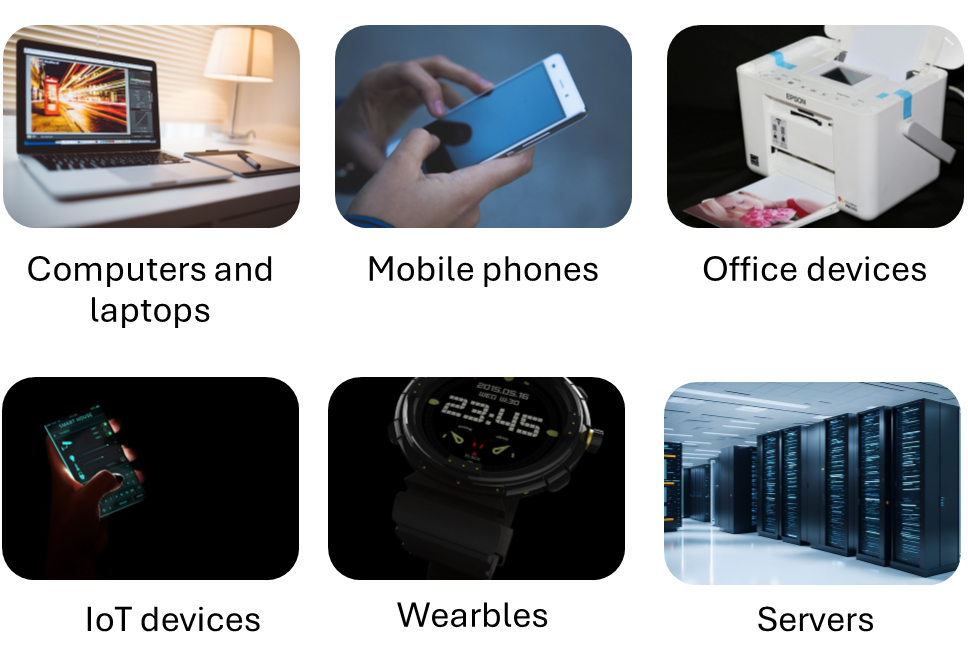
Endpoint devices encompass any devices capable of connecting to the central business network. These devices, such as desktop computers, laptops, connected devices, mobile phones, and wearables, serve as potential entry points for cybersecurity threats. Ensuring robust protection for these endpoints is crucial, as they often represent the weakest link in network security. Beyond computers and mobile devices, office equipment like printers, faxes, smart devices, and other appliances connecting to the network also pose potential vulnerabilities and demand protection. Servers, storing or processing business data, emails, and documents, are traditional yet critical endpoints that require special emphasis on security measures.
How does endpoint protection work?
Endpoint security safeguards an organization’s endpoints by deploying an Endpoint Protection Platform (EPP) on devices to thwart potential infiltrations by malware or other tools. The platform, which can be implemented on-location, in the cloud, or through a hybrid model, enables administrators to monitor, investigate, and respond to cyber threats effectively. Cloud-based solutions are more popular due to their scalability and efficiency. They also free endpoints from the burden of locally stored threat databases.
In terms of functionality, endpoint security software typically includes:
- Machine learning for zero-day threat detection
- Integrated firewalls
- Email gateways to combat phishing
- Insider threat protection
- Advanced antivirus and anti-malware tools
- Proactive security for safe web browsing
- Encryption for endpoint, email, and disk protection
The goal is to offer administrators a centralized platform, enhancing visibility and simplifying operations, allowing swift threat isolation.
The concept of Endpoint Detection and Response (EDR) is often associated with endpoint security. EDR enables the identification of sophisticated threats like polymorphic attacks and zero-day threats through continuous monitoring, providing enhanced visibility and enabling quicker response times for threat containment. Modern endpoint security platforms frequently integrate both EPP and EDR functionalities to provide comprehensive protection against a range of cyber threats.
Endpoint protection platforms are much beyond traditional antivirus solutions in several ways. Unlike antivirus programs that focus on a single endpoint, EPPs provide visibility into the entire enterprise network from a centralized location, enhancing comprehensive security. They also streamline administration responsibilities by moving away from user-dependent manual updates by offering automated updates. This ensures continuous and up-to-date protection with the incorporation of advanced threat detection methods like behavioral analysis.
Use cases of endpoint security
1. Securing Mobile Devices – With the BYOD policy being adopted at workplaces, there is a surge in mobile devices utilized for work. Unlike traditional endpoints, mobile devices feature less secure digital perimeters and connect to various networks, necessitating EDR to extend consistent security across all connected devices, ensuring comprehensive network visibility and protection.
2. Addressing the Evolving Threat Landscape – The evolving threat landscape requires a shift from traditional antivirus models to endpoint protection systems as cyber threats constantly innovate. Antivirus struggles to keep pace, prompting the need for a detection and response approach. EPP identifies threats that breach the cybersecurity perimeter and focuses on timely detection and response rather than solely preventive measures.
3. Improving Threat Investigation – In the context of modern cybersecurity, investigating threats becomes intricate. EDR solutions with alert capabilities play a pivotal role in directing investigations and enhancing detection and response times. These tools prove essential for efficiently managing IT environments with diverse devices and contribute to effective threat hunting.
4. Enhancing Cloud Security – The adoption of cloud computing has revolutionized software companies by offering cost-effective solutions and eliminating the need for managing local servers or data centers. However, this shift introduces complexities in security, as each access level in the cloud architecture becomes a new endpoint requiring protection.
5. Safeguarding IoT Devices – The Internet of Things (IoT) presents unique challenges to security, with many devices lacking sufficient cybersecurity measures. Endpoint detection and response mitigates this vulnerability by extending security protections to all devices, including IoT devices, closing potential security gaps and protecting against cyber threats.
6. Monitoring Network Performance – Endpoint security plays a crucial role in monitoring network performance and security, with sensors at the edge and nodes continuously generating data logs. These logs assist organizations in identifying anomalous behavior, and suspicious activities, and optimizing capacity and resource allocation, ensuring the availability and performance of business services.
7. Scaling Business Services – Endpoint security solutions enable organizations to add value by reprogramming endpoints to reach a wider user base. This flexibility allows businesses to tailor, update, and improve services based on evolving end-user responses, showcasing the adaptability and scalability that EDR brings to modern business services.
Selecting the right endpoint security solution for your business
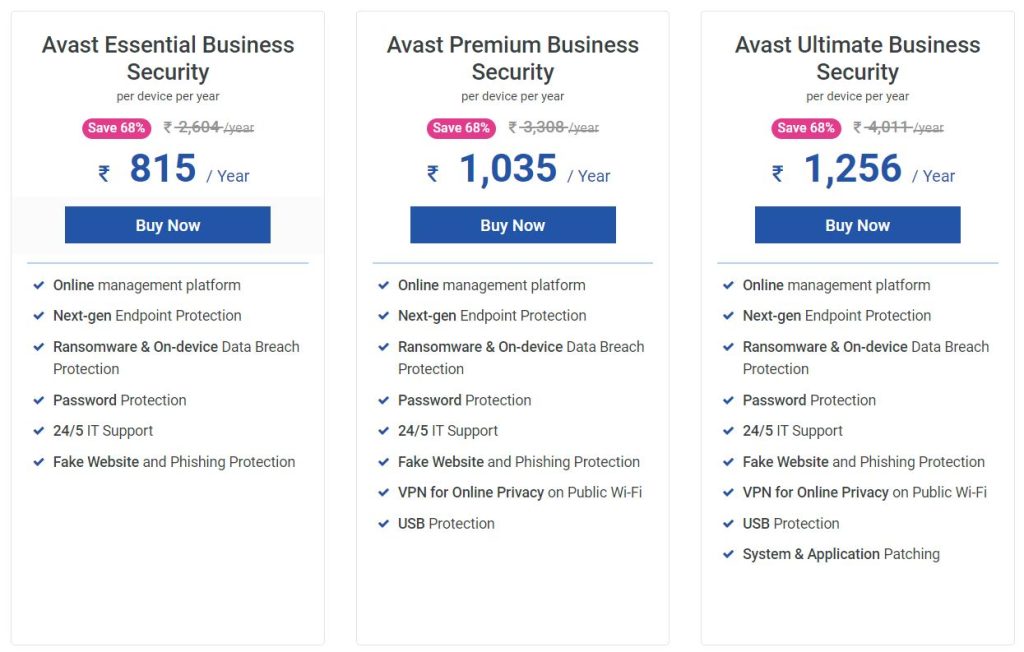
Choosing the most suitable endpoint security solution depends on your specific requirements. It is crucial to evaluate the included protections and choose a suite that aligns with your size and budget.
Avast endpoint security solutions from ZNetLive offer advanced multi-layered security, safeguarding devices with six layers of robust defense against malware, ransomware, and sophisticated cyberattacks in real time. Avast antivirus provides multiple layers of defense against harmful files, emails, and websites. The system ensures prompt communication of signals, offers actionable recommendations, and allows users to dismiss or temporarily silence alerts, with a comprehensive alert history available to all users.
Plans start from INR 815 per year, providing budget-friendly, comprehensive online protection to ensure digital safety without compromise.
Book a demo now to experience the full spectrum of features and enhance your cybersecurity posture.
Featured image: Freepik
Read next: 7 Must-follow Tips for Data Leakage Prevention (DLP) in 2024