Network infrastructure design is very important for setting the blueprint for smoothly running various operations within the hardware and software systems of the company. It is like a laid down map, with proper directions to facilitate a journey; in IT fraternity what we call the systematically distributed layers between hardware and software system of an organization. An ideal network infrastructure management model will give you maximum flexibility, scalability and reliability.
Cloud service providers and data center managers have always been looking for that ideal network architecture which can help them in efficiently organizing their operations and rendering better services to their end users. Here, we are going to discuss one of the most followed network models for cloud and DC management that is “Hierarchical Network Design.” What is it? And how it helps you in reforming your network components, let’s find out:
Hierarchical Network Design

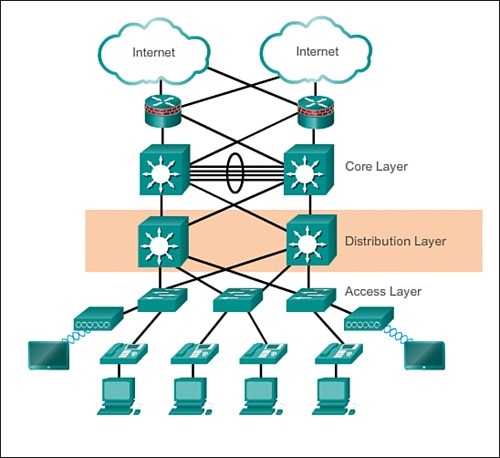
A hierarchical design represents a network which is divided into several discrete layers. Here each hierarchical layer has well-defined role and functions within the overall network architecture. This type of division helps the network designer to optimize and pick the suitable hardware and software and define their roles for that particular network layer.
This applies to both LAN and WAN. It surpasses the demerits of a flat network design, by providing flexibilities to control increasing demands of the applications.
A hierarchical LAN network design, typically includes the following layers:
- Access Layer,
- Firewall,
- Distribution layer,
- Core Layer.
1. Access Layer
As the name suggests, access layers are there to grant access to the end devices and users. In a LAN network, this access is given to the end users, as against the WAN network, wherein the remote users are given access to a corporate network having WAN connections. The following figure shows the layout of the access layer in the overall network model.

It plays an important role by:
- Ensuring high availability.
- Giving port security.
- ARP (Address resolution protocol) inspection.
- VACLs (Virtual access control lists).
- Spanning tree.
- QoS classification.
2. Distribution Layer
A distribution layer combines the incoming data from the access layer and then the data is transmitted to the core layer, from where it is routed to its final destination. As shown in the figure, distribution layer stands as the boundary line between the layer 2 domains and the routed network of layer 3.
It is the main point in the wiring closets. It may also provide upstream services to various access layer switches. It plays an important role by:
- Playing as the combination of LAN and WAN links.
- ACLs and filtering forms for policy-based security.
- Load balancing and redundancy.
- Routing, aggregating and summarization is configured on interfaces to core layer, by playing the role of a boundary.
- Broadcasting domain control.
3. Core layer
Considered as the network backbone, it includes high-speed network devices, to fasten up the process of switching packets and interweave various campus components. Campus components may include service modules, distribution modules, the DC and the WAN edge. As shown in the figure, the core layer is important to maintain the interconnectedness between various modules of the distribution layer.

It plays an important role by:
- Providing high-speed connectivity, and package switching.
- Fault tolerance capability making it most reliable.
- Scales faster with less equipment.
- Saves CPU intensive manipulation driven by QoS, security, inspection and other processes.
4. Transparent Firewall
A firewall traditionally played a routed hop and acted as a gateway for hosts which connected to any of its screened subnets. But, a transparent firewall behaves differently. It is a Layer 2 firewall and acts as a “stealth firewall” or “a bump “in the connection. Unlike a router hop, it cannot be seen connected to the device.

One of its major benefits is the ease of installation. The transparent firewall can be easily integrated into your existing network infrastructure through the ASA, as it can connect various subparts of a network.
However, these days, organizations are also looking forward to adding a FortiGate in transparent mode, to secure private connections to the internet. When in transparent mode, the FortiGate, without applying routing, directly applies security scan to the traffic. The major benefits of installing a FortiGate unit in the transparent mode is that:
- You can browse the internet through any computer, which is connected to FortiGate’s internal interface.
- You can get information about the traffic that is being processed by the FortiGate.
The security layers like “transparent firewall”, are making data center infrastructure management easy and reliable. An ideal DC or CSP should try to follow an efficient network architecture. With technology taking huge steps each day, from traditional router firewall to transparent level 2 firewall, we can see the emerging changes.
The reason? Undoubtedly the quest for better network management.
We hope this write-up will help you in selecting the perfect network infrastructure model for your organization. Feel free to share your views, in the comments section below.
Services ZNetLive offer: