- December 1,2016: Rahul Gandhi’s Twitter handle hacked; abusive tweets flow.- Times of India.
- December 15, 2016: Yahoo reveals new hack, this time a billion plus users. – The Economic Times.
Prominent personalities like Rahul Gandhi, Vijay Mallya, Ravish Kumar and Barkha Dutt were all in the news few weeks back, as their twitter accounts were hacked by Legion, an unknown group of people. Similarly, Yahoo too confirmed that its over 1 billion user accounts were compromised in the largest data breach till now.
There are over one billion websites, currently operational on the internet today and this number is increasing every second due to –
- Rise in the number of tools and platforms that have made it easier for us to have an online presence.
- Rise in Content Management Systems (CMS).
Over a third of the websites online are powered by five key CMS platforms: WordPress, Joomla, Drupal, Magento and Blogger.
WordPress is leading the CMS market with over 58.5% market share (used by 27.3% of all the websites)– W3 Techs Survey.

However, this increased user adoption is equally responsible for the rise in the number of low-skilled and poorly equipped service providers and webmasters, who while deploying and administering the sites, don’t take adequate measures to prevent phishing, malware and hacking from compromising credibility and security of your websites.
Why CMS platforms are vulnerable to hacking?
A Content Management System is a software application that helps in the administration of the digital content- be it videos, images, documents or any type of online content.
But CMS with widely publicized vulnerabilities within them, prove to be a goldmine for script kiddies and one of the most common hacking targets in the web world.
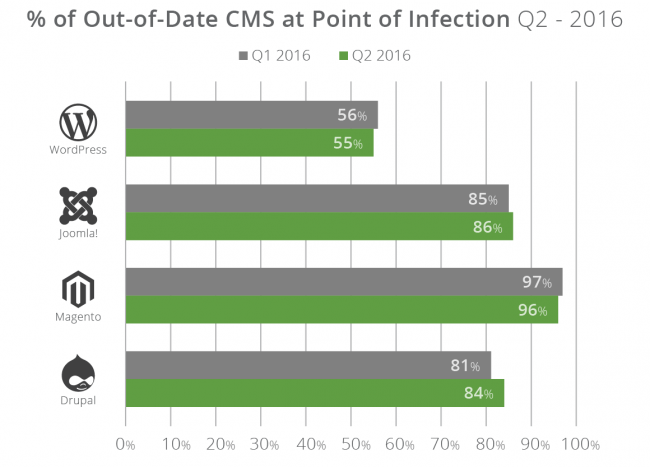
As per the Sucuri Security’s Website Hacked Report 2016-Q2, the four CMS platforms most affected by the hacking are WordPress and Joomla! followed by Magento and Drupal.

There is a combination of factors that makes CMS vulnerable to hacking attacks. The leading causes of CMS platforms getting hacked are: –
- Open source nature – Unlike closed source/proprietary software, the transparent nature of open source software allows easy inspection and modification of the source code, as it is free and publicly accessible. Thus, although CMS built on an open source framework supports collaborative environment -multiple users working, sharing and modifying the source code together, it is more vulnerable.
- Predictable and crackable passwords – Not every key can slide into the keyway of a lock. Similarly, every logon process has its unique password that establishes ‘who you are’.Hackers can use this valuable resource to breach the security and gain an advantage, if the password is easy to crack. CMS like WordPress includes an administrator user account with username as ‘admin’- thus, giving an advantage to hackers of easy login.Also, many website operators using WordPress web hosting unknowingly leave their administrator accounts vulnerable to brute force attacks by using weak or crackable passwords, which hackers can easily use to inject malware, turning websites into distributed denial of service (DDoS) bots.
- Use of protocols – WordPress and other CMS platforms use a protocol -XML-RPC to provide services such as pingbacks, trackbacks and remote access to users but the hackers can use this to initiate DDOS attacks.
“26,000 different WordPress sites were exploited to launch Layer 7 distributed denial of service (DDoS) attacks” – Sucuri, Security Research Firm.
- Insecure extensible components – Cross site scripting and SQL injection are the most popular infection types in various CMS plugins, themes, modules, templates and other integrations.
The biggest risk comes from the installed plugins and themes. If their vulnerabilities are not fixed timely, then they become an easy way of exploitation by the hackers.
- Continuing using outdated versions – According to BSI, “CMS should never be run in its default configuration and should be upgraded whenever newer versions become available”.But administrators, while upgrading the main system, often forget to update add-ons, thereby leaving space for vulnerabilities.
Steps you should take to secure your website from hacking.
- Keep your installed scripts and CMS platforms up- to- date (newest versions). Schedule regularly an update or patch the CMS, along with all components like installed plugins and themes.
- Perform backups regularly for the CMS in use and its underlying database, weekly at a minimum.
- Opt for a Web Application Firewall (WAF), the enterprise-grade website security product, which automatically protects against all vulnerabilities.
- Install security plugins to actively prevent hacking attempts. These plugins notify the weaknesses inherent in each platform and foil the hacking attempts that could threaten your website.
- Use parameterized queries and prevent entry of rogue code into your query that could be used to change tables, get information and delete data.
- Use strong passwords for your website’s admin area and server to fight against the brute force attacks. Always store passwords as encrypted values and change your passwords regularly to keep them doubly secure.
- Install SSL on your web server. SSL is the technology that establishes a secure connection between your server and the browser. Always use a security certificate for your website and gain customer trust.
- Test your website security via the use of some website security tools like Netsparker, OpenVAS etc.
- Fortify your admin directories to prevent hacking into them. Rename your admin folders to the name of your choice, only known to your webmasters to reduce potential breach possibility.
Hope the above mentioned security tips will help you secure your website against the hackers. Don’t sit with the thought that “it cannot happen to me”. Prevention is always better than cure.
Services ZNetLive offer:
Managed WordPress Hosting Plans
Share your doubts and of course security tips if you have any, via comments.
Source:
- http://timesofindia.indiatimes.com/india/Rahul-Gandhi-Twitter-handle-hacked-abusive-tweets-flow/articleshow/55710225.cms
- http://economictimes.indiatimes.com/tech/internet/yahoo-says-1-billion-accounts-exposed-in-newly-discovered-security-breach/articleshow/55991332.cms
- Source- Website Hacked Trend Report 2016-Q2



I am lucky to find this site! Interesting.