Financial Institutions are actively using the cloud to digitize their business operations and leverage the cost efficiencies offered by the cloud. In a recently conducted study, Amazon Web Services (AWS) was identified as the primary cloud provider in the financial sector with 45% of respondents saying they use AWS Cloud(*). However, with increased digitization, the risk of cyberattacks on financial institutions is also rising. Companies need to follow AWS Security Best Practices to leverage the most out of their move to the cloud while keeping the data secure.
Introduction
The past decade has seen steady growth in cloud adoption. The COVID-19 pandemic and remote work trends have further reaffirmed the need for organizations to be digital.
However, as cloud adoption rises, there also has been an increase in talks around cloud security – especially in public and multi-cloud environments. 45% of businesses have experienced a cloud-based data breach or failed audit in the past 12 months – as per a study published in 2022.
For any organization, using a public or multi-cloud environment, understanding cloud security, and taking measures to secure the cloud are important for protecting against data breaches and losses. In this article, we will be focusing on the AWS Security best practices for Banking, Financial Services, and Insurance customers.
Why AWS?
AWS has established itself as the market leader in the cloud infrastructure segment with 34% occupancy. It is one of the most popular clouds – closely followed by Microsoft Azure and Google Cloud.
Over the years, AWS has played an important role in facilitating digital transformation in various banks and other financial institutions by offering a secured, reliable, and resilient cloud infrastructure. Some of the popular finance institutes using AWS Cloud include Capital One, Nasdaq, Stripe, Thomson Reuters, Coinbase, etc.
Fintech institutes and startups can leverage the cost-effective solutions offered by AWS to build on cutting-edge technologies like blockchain, web, mobile applications, etc. It helps them move from the CAPEX-intensive model to an OPEX model of operations. Also, it provides a seamless and safe data backup option in the cloud for financial transactions and data. Apart from the cost efficiency and OPEX-focused model, the cloud has also helped financial institutions to deliver digital customer experiences at a minimal cost.
AWS Security – why does it matter?
AWS security presents both opportunities and challenges to organizations that utilize the cloud platform.
While AWS has a strong focus on ensuring cloud security for its customers – it is never a one-sided responsibility, consider it more of a shared responsibility. This means, while Amazon takes all measures to secure your cloud environment, you too should have security controls in place for the applications and data you deploy on the cloud.
AWS cloud security is a wide concept – however, to cover the basics, you should at least focus on three questions:
- Who can access your applications?
- Is there any log monitoring in place for tracking file changes?
- Does your organization follow a strong password policy and authentication practice?
The major risks in the AWS cloud environment can be unauthorized cloud access, misconfiguration, insecure interfaces, account hijacking, lack of logging and monitoring tools, disabled multi-factor authentication, lack of permission control for S3 buckets, and machine state snapshots in public storage.
It is important to note that AWS covers various tools and solutions in AWS security services. But many organizations might fail to implement these controls and thus make their data vulnerable.
Another challenge is the inability to develop strong strategies for data protection in the cloud and ensure compliance with relevant industry regulations. This is especially true for financial institutions – as there are many regulations to meet. Effective AWS security requires you to plan on capitalizing on the advantages of the cloud to stay informed about a range of best practices and new technologies currently available.
What are the AWS security risks for financial institutions?
The financial sector is a hot target for cybercriminals – primarily due to the volume of critical information they carry – bank account usernames, passwords, account numbers, and more.
- In the first half of 2021 alone ransomware attacks in the banking industry increased by a whopping 1318% which was disproportionate to other industries – as per a report.
- In another report, U.S. banks processed roughly $1.2 billion in ransomware payments in 2021.
- The New York Federal Reserve noted a report that financial firms experience cyber-attacks 300 times more than other industries – highlighting how attractive this sector is to cyber criminals.
With banking technology and the complexity of financial regulations changing rapidly, institutions must keep up and mitigate risk to protect customers and their data.
Cybersecurity threats such as malware, data theft, and social engineering are among the biggest risks facing financial services firms today.
The risks have further increased as transactions are becoming more cashless or digital.
However, despite the risks, cloud security is still a challenge for the finance sector. Many banks do not seem to understand where their cloud infrastructure risks lie. Lack of IAM (Identity and Access Management) controls, misconfigurations of the cloud environment, and lack of visibility and monitoring, are other challenges that banks face when it comes to cloud security.
Additionally, poor internal processes can lead to financial losses through mishandling transactions or fraud. To remain secure, banks must develop consistent policies and procedures for protecting all forms of customer data, identifying, and responding to cyber threats, and minimizing internal errors.
AWS security best practices for BFSI
1. Establish an effective AWS Cloud Governance strategy
Through the AWS Cloud Governance service, you can establish policies and procedures for the effective use of your AWS cloud environment. You can set up guidelines to define who can access resources, the types of resources that can be accessed, and define rules for managing resource costs.
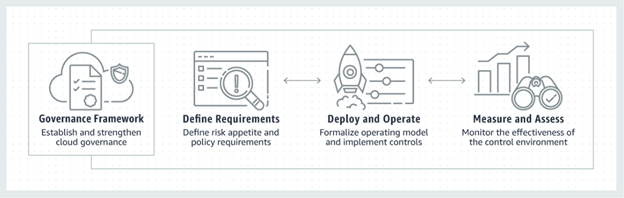
It is a great way to have deeper visibility and control of your AWS cloud usage. It will help you minimize risk, increase security, protect sensitive resources and data, and ensure compliance with applicable laws and regulations.
2. Protect your infrastructure with the Amazon Web Application Firewall
The Amazon Web Application Firewall (WAF) provides you with a cloud-generated method of protecting your web infrastructure from malicious cyberattacks. The advanced security features on AWS WAF can help pinpoint potential rule violations and quickly detect potential threats.

3. Review and define AWS Security Groups for your EC2 instances
Amazon Security Groups are virtual firewalls that act as a defense for your EC2 systems. They can help you control incoming and outgoing traffic. Whenever you launch an EC2 instance, you can specify one or more security groups and apply rules for outbound and inbound traffic. All traffic that reaches an instance is evaluated through these rules.
They are one of the tools that AWS offers for securing instances – however, you need to configure them to meet your unique security needs. Most of the security groups come with default settings. If you fail to monitor groups individually, you might risk your application data.
The security groups are available for both Windows and Linux EC2 instances.
4. Manage security by leveraging the AWS Security tools
Managing the security of an organization’s information technology and cloud resources can be a complex and daunting task. Fortunately, Amazon Web Services (AWS) makes the job easier by providing users with a vast selection of security monitoring tools.
Some of the most popular ones include:
AWS CloudTrail: This tool can be used to monitor AWS deployments by getting a history of API calls for your account. It also helps you identify the users and accounts who called for the APIs.
Amazon CloudWatch: It is probably the easy-to-use cloud monitoring solution by AWS that is reliable, flexible, and scalable.
Amazon GuardDuty: This threat-detection service by AWS helps you monitor malicious activity and unauthorized behavior to protect your AWS accounts and workloads. The above solutions provide security to your AWS accounts. AWS also offers tools to protect your applications like the AWS Web Application Firewall (which we discussed above). Other tools include Amazon Inspector, AWS Shield, and AWS Secrets Manager.
5. Monitor regularly with AWS Security Hub
AWS Security Hub is a powerful platform for monitoring and managing security within Amazon Web Services (AWS) environments. It provides continuous assessment of your organization’s resources through the automated collection, analysis, and integration of potential security issues to identify potential risks and meet compliance requirements.
It also gives you visibility into your logs, alerts, and other types of data related to potential security incidents. Thanks to this powerful dashboard you can take appropriate action quickly in case of any breach.
6. Limit S3 Bucket Permissions
Amazon S3 storage is a popular service among Financial Services Institutions (FSIs). It helps them collect large volumes of data from sources like customer transactions, customer service engagements, chat transcriptions, etc. It is a highly secure service. But to leverage its full benefits and security features, you must make use of S3 tools offered by Amazon to help you monitor and manage security policies. Features like Block Public Access, Encryption and Key Management tools, and other audit and governance tools can help you enhance the security of your S3 buckets.
7. Set up strong Authentication Policies using IAM
AWS Identity and Access Management service will help you protect your AWS resources in the cloud. With this, you can create user roles and assign permissions to specific resources in your AWS environment.
It is further backed by multi-factor authentication and Single sign-on access to secure and centralize user access. Note that IAM is an account security protocol.
AWS allows you to set various policy types and attach them to IAM identities. You can set up Identity-based policies, permissions boundaries, resource-based policies, access control lists (ACLs), organization service control policies (SCP), and more.
8. Adhere to regulations with AWS Compliance Center
AWS compliance center is an important platform for businesses to make sure they are adhering to regulations and security protocols. Companies that use the AWS environment can put their minds at ease knowing that it meets a wide array of compliance standards.
The center clearly details compliance frameworks, such as FedRAMP, PCI DSS, GDPR, and HIPAA; offering example controls that can help companies identify potential areas of non-compliance risks.
AWS Security Best Practices – Conclusion
AWS provides customers with a great deal of control over their security. However, as with any large and complex system, there are always potential security risks.
By following the AWS Security best practices outlined in this blog post and making use of AWS security services, you can keep your AWS environment safe and secure. Additionally, it is always a wise practice to choose an expert cloud service provider when moving to AWS Cloud. The right technology partner can help you migrate to AWS Cloud seamlessly and take measures to improve its security and compliance requirements.
If you’re worried about the security of your AWS Cloud or want to know more about it, you can get in touch with our AWS experts at sales@znetlive.com.
As always, if you have any questions or comments, you can let us know in the comments section below.
Read Next: 10 futuristic services you don’t know exist in AWS
Sources:


