-
-
-
- Resources
-
 Customers purchase products with digital discovery. Get listed on the go-to marketplace where customers discover new-age software solutions.
Customers purchase products with digital discovery. Get listed on the go-to marketplace where customers discover new-age software solutions.- B2B Marketplace Expand Business Horizons
- Billing Management Maximize Revenue with Simplicity
- Provisioning Automation Automate Deployments, Scale Faster
- Order Management Efficient Order Processing
- Customer Self-Service Panel Enable Seamless Customer Self-Service
- Multi-tier partner management Efficiently Manage Partner Networks
- Support Process Management Enhance and Streamline Support Workflows
- Affiliate Marketing Platform Boost ROI with automation
- Business Intelligence Real-time insights for growth
- Marketing AutomationAutomate, engage, and convert
- Business AccelerationAccelerate growth and expand
- Business Facilitation Services Powering cloud business success
- About us
- Partner with us
Free Sign Up
- Access to free tools
- Early access to deals/offers
- Free access to exclusive resources
To know the current status of your order, please fill the following details:
Revamp Remote Work Security with InstaSafe
The ideal security solution for modern hybrid workforce. Scalable security that caters to the requirements of enterprises of any size. Get single click access to applications with zero trust security framework.
- Improved security, user experience, and simplicity
- Zero trust for multi-cloud, no legacy hassles
- App access control, visibility, secure connectivity

Rethink Security for your Remote Workforce
For 'Work from Anywhere', security is the need of the hour

Secure Remote Access
- Protect and Enable Access for on-prem applications
- Integrated Single Sign On (SSO) for a seamless access experience
- Natively secure all cloud applications
- Secure access to internal web applications
- Secure remote access to SSH/RDP
- Separate data and control traffic
All round visibility
- Monitoring of user activity from Single Pane Command Dashboard
- Multiple cloud-based applications accessed through single click
- Choose between agent based, agentless, and secure workspace browser options for deployment
- Disable Screen capture, Copy/Paste & Clipboard
- Disable Screen Recording
- Block downloads for sensitive applications


Upgrade existing Security Posture
- InstaSafe Gateway only visible to user device
- Secures against DDoS Attacks
- Separate user and group level access policies
- MTLS Encryption of traffic
- Drop All Firewalls
- Separate encrypted tunnel for each application connection
- Conceals itself, applications, and devices from internet
Granular Access Control
- Enforce role-based access policies
- Set granular level policies for BYOD devices
- Geolocation and Geobinding - restrict access based on location of user and device
- Enable behavioral biometrics for privileged users accessing critical data
- Carry forth device posture checks before granting access


Endpoint Capabilities
- Behavioral Biometrics based authentication
- Device Posture and User Identity Checks
- Disable Screen Recording
- Block downloads for sensitive applications
- Dynamic Authorization based on Geo-risk and Temporal (Time based) Risk Assessment
- One click access to applications on a single Dashboard
- Disable Screen capture, Copy/Paste & Clipboard
Seamless Integrations
- Disable Screen Recording
- Easy Integration with 3rd party applications
- SAML/AD Integration
- Seamless Integration with SIEMs and reporting tools
- TOTP Authentication
- Inbuilt InstaSafe Authenticator
- Log streaming services
- Inbuilt IDP with support for LDAP/AD

Why Zero Trust with InstaSafe?
Eliminate the need for VPNs and obsolete security tools
Simplify deployment and maintenance with a hyperscalable SaaS solution that doesn't need complex firewalls.

Reduce your attack surface
By enabling the least privilege access model, grants access to users and devices following continuous verification.

Stop cyberattacks
By reducing the attack surface and utilizing a continuous risk assessment system, stop insider threats and common cyberattacks.

Reduce cost of IT
Reduce total cost of operations by as much as 40% by deploying hardware free solutions.

Monitor all Access
Manage and monitor all user activities and access to the cloud and on-premise applications from a single dashboard.

Work from Anywhere
Manage access to all your applications from an easy-to-use console. Enable employees to work safely from anywhere without worries related to compromised networks.

Replace your VPN
InstaSafe enables secure access to applications of any kind, to workforces situated anywhere. Compared to legacy solutions like VPNs, InstaSafe minimizes attack surface and prevents malicious actors from gaining insider access to sensitive resources.

Manage Vendor Access
With advanced monitoring and authentication features, and all-round visibility over all user activity, privileged access of resources to third party contractors using unmanaged devices becomes simple and easy.

Secure On-Premise and Cloud Applications
Instead of relying on multiple tools to access on-premise and cloud workloads, simplify access and prevent the risk of lateral movement with InstaSafe.

Identity Based Verification
Access is based on user identity authentication and device posture assessment that’s done continuously.
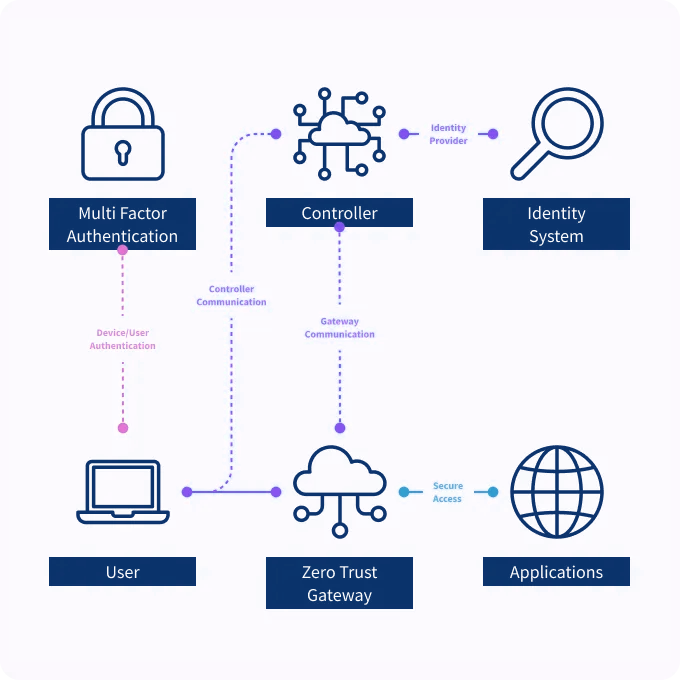
How InstaSafe works?
Three-dimensional risk assessment methodology – user, device, and application
InstaSafe uses 4 core principles to work

Innate distrust, default deny
Operationalize a system of continuous authentication and authorization to provide least privilege, contextual access.

One Size doesn’t fit all
Complete visibility and control over user activity allows for framing access policies on a granular level, and restricting access based on different levels of privilege for different users.

Align and Integrate
Align to a broader security strategy and allow for easy integration with other security tools for better security posture.

Security based on Identity
Pull the security perimeter from the network to the individual human users, and grant access based on identity as the single control point.
Device and User Authentication
- Device and user identity get authenticated by the Controller through Multi factor Authentication (MFA).
Gateway and Controller Communication
- Controller communicates with the Gateway and requests access for the legitimate user.
User Device and Gateway Communication
- mTLS tunnel is established between Gateway and device for allowing data traffic for permitted application access.
50K+ Businesses Trust ZNetLive for their IT needs
-
The move to AWS (Amazon Web Services) Cloud was the best decision, undoubtedly. ZNetLive further simplified the entire process by helping our team set up our systems on AWS Cloud.
Mr. Satish Jain
AGM - Business Transformation,
B. Lal Clinical Laboratory Pvt. Ltd.
After using AWS from ZNetLive, we do not have to think any more about building and operating the infrastructure. The most important benefit is we can now focus on our time, money, and energy to create great experiences for our customers.
Mr. Siddharth Ajay Singh
Managing Director and CEO Jumbo Finvest India Ltd.

-
By providing Microsoft’s Office 365 solution, ZNetLive addressed all our security requirements and confidentiality of our communication through mail along with features like web conferencing, enhanced mailbox size and more at much lesser price than Google apps we were using.
Mr. Satyendra Johari
MD, Johari Digital Healthcare Limited.

The move to AWS (Amazon Web Services) Cloud was the best decision, undoubtedly. ZNetLive further simplified the entire process by helping our team set up our systems on AWS Cloud.
Mr. Satish Jain
AGM - Business Transformation,
B. Lal Clinical Laboratory Pvt. Ltd.
ZNetLive is a leading provider of cloud computing services, empowering businesses to create abundance through scalable, secure, and reliable technology. We support over 50,000 customers worldwide with solutions purpose-built for sustainable growth, operational resilience, and long-term business value.
With 24/7 expert support, we ensure your IT ecosystem stays resilient, future ready, and aligned with your business goals, so you can focus on growth while we handle the technology.
FAQs
-
What is the use of InstaSafe?
InstaSafe is a comprehensive security solution designed to protect your network and data in a hybrid work environment. It ensures secure access for remote users, safeguards sensitive information, and minimizes the risks associated with cyber threats. -
How to install InstaSafe?
Installing InstaSafe through ZNetLive is a seamless process. Our team of experts will guide you through every step, ensuring a hassle-free setup. Once you've acquired InstaSafe services from ZNetLive, our professionals will assist you in the installation process, configuring the application to suit your hybrid work environment's specific needs. With our dedicated support, you'll have InstaSafe up and running smoothly in no time. -
How can I download InstaSafe?
To access InstaSafe's powerful security solutions, simply acquire the services from ZNetLive. Upon purchase, you'll gain access to the necessary download links and resources. Our team will ensure that you receive all the information required to download InstaSafe according to your hybrid work environment's requirements. -
How does InstaSafe protect my network layer?
InstaSafe safeguards your network layer through a comprehensive Zero Trust security approach. It employs authentication, authorization, segmentation, and continuous monitoring. Beginning with device classification and policy creation, InstaSafe ensures that only authorized users and devices can access your network resources. By translating policies into specific commands for network devices, it enforces granular access control. Additionally, the use of Software Defined Perimeters ensures that each access request is evaluated independently, with user traffic securely tunneled through application-specific channels. This layered strategy, coupled with continuous monitoring, minimizes the risk of unauthorized access and strengthens your network's security. -
Does InstaSafe Secure Access support 2FA?
Yes. InstaSafe Secure Access offers integrated Two-Factor Authentication (2FA) via SMS, Email, or Google OTP. We also extend compatibility to third-party token-based solutions like RSA SecurID and Vasco through the RADIUS protocol. Furthermore, our proprietary Authenticator Application enhances your enterprise security with features spanning from TOTP-based authentication to biometric-enabled access, providing an extra layer of protection.